What Makes a Password Truly Secure?
A secure password has two fundamental properties: sufficient length and sufficient entropy. Entropy is a measure of unpredictability — the higher the entropy, the more combinations an attacker must try to crack the password by brute force. This generator uses the Web Crypto API's crypto.getRandomValues() to produce passwords with maximum cryptographic entropy.
The most common password mistakes are not using weak characters — they are using too few characters and reusing passwords across services. A 24-character random password using all character sets has approximately 157 bits of entropy, making it computationally infeasible to crack with any current or foreseeable hardware.
How Password Entropy Works
Password entropy is calculated as: entropy = length × log₂(charset_size). The charset size depends on which character types you include:
- →Lowercase only (a-z): 26 characters → 4.7 bits per character
- →Lowercase + uppercase (a-z, A-Z): 52 characters → 5.7 bits per character
- →Alphanumeric (a-z, A-Z, 0-9): 62 characters → 5.95 bits per character
- →Full charset (a-z, A-Z, 0-9, symbols): ~94 characters → 6.55 bits per character
A 16-character password with the full charset has ~105 bits of entropy. A 24-character password has ~157 bits. For context, cracking a 128-bit key with current hardware would take longer than the age of the universe.
Cryptographic Randomness vs. Math.random()
Most password generators on the web use JavaScript's Math.random() — a pseudorandom number generator (PRNG) that is not cryptographically secure. Its output is deterministic and predictable if an attacker knows the seed or observes enough output values.
This generator uses window.crypto.getRandomValues() — the Web Crypto API's cryptographically secure random number generator (CSPRNG). It is the same source of randomness used by TLS, SSH key generation, and browser security. The output is statistically indistinguishable from true randomness and cannot be predicted or reproduced.
The generator also uses rejection sampling to eliminate modulo bias — a subtle flaw where some characters appear slightly more often than others when using the modulo operator to map random bytes to a charset. Every character in the output has exactly equal probability.
Password Length Recommendations by Use Case
User Account Passwords — 16 to 24 Characters
For website and application logins, 16–24 characters with all character types provides more than sufficient security. Since you will store these in a password manager, length is not a usability concern. NIST SP 800-63B recommends a minimum of 8 characters but notes that longer passwords are significantly more secure.
API Keys and Secrets — 32 to 64 Characters
API keys, OAuth secrets, webhook signing secrets, and encryption keys should be at least 32 characters of alphanumeric characters. Many services use 40–64 character hex strings (equivalent to 160–256 bits of entropy). Use this generator with numbers and letters, 32–64 characters, for production API secrets.
Database Passwords — 24 to 32 Characters
Database credentials should be long and complex since they are stored in configuration files and environment variables, not typed manually. 24–32 characters with all character types is appropriate. Avoid characters that require escaping in shell scripts ($, `, !) if the password will be used in shell commands.
Encryption Keys — 32+ Characters (Hex)
For AES-256 encryption keys, you need exactly 32 bytes (256 bits) of random data. Generate a 64-character hexadecimal string (using numbers 0-9 and letters a-f) for a properly formatted 256-bit key. For JWT signing secrets, 32+ alphanumeric characters provides sufficient entropy for HS256.
Password Hashing — Never Store Passwords in Plain Text
When building applications that store user passwords, never store the raw password — always hash it with a purpose-built password hashing algorithm:
- →Argon2id — The winner of the Password Hashing Competition (2015). The current best practice. Memory-hard, resistant to GPU and ASIC attacks. Use this for new applications.
- →bcrypt — Battle-tested since 1999. Widely supported across all languages. Use a cost factor of 12 or higher for modern hardware.
- →scrypt — Memory-hard like Argon2. Used by many cryptocurrency wallets. Good choice when Argon2 is not available.
- →PBKDF2 — NIST-approved and FIPS-compliant. Required in some regulated environments. Use with SHA-256 and at least 600,000 iterations.
Never use MD5, SHA-1, or SHA-256 directly for password hashing — these are fast hashing algorithms designed for data integrity, not password storage. They can be cracked with GPU-accelerated dictionary attacks in seconds.
Password Manager Integration
The only practical way to use unique, high-entropy passwords for every service is a password manager. The most trusted options are:
- →Bitwarden — Open source, self-hostable, free tier available. Recommended for developers.
- →1Password — Excellent team features, Travel Mode, and developer integrations (SSH keys, CLI).
- →KeePassXC — Fully offline, open source, no cloud dependency. Ideal for high-security environments.
Generate a password here, copy it, and save it directly to your password manager. Never type generated passwords into a browser's autofill — paste them to avoid keylogger exposure.
Multi-Factor Authentication — Beyond Passwords
Even the strongest password can be compromised through phishing, data breaches, or social engineering. Multi-factor authentication (MFA) adds a second layer of verification that an attacker cannot obtain from a stolen password database.
The most secure MFA methods in order of strength: hardware security keys (FIDO2/WebAuthn, e.g. YubiKey) → authenticator apps (TOTP, e.g. Authy, Google Authenticator) → push notifications (e.g. Duo) → SMS codes (least secure, vulnerable to SIM swapping).
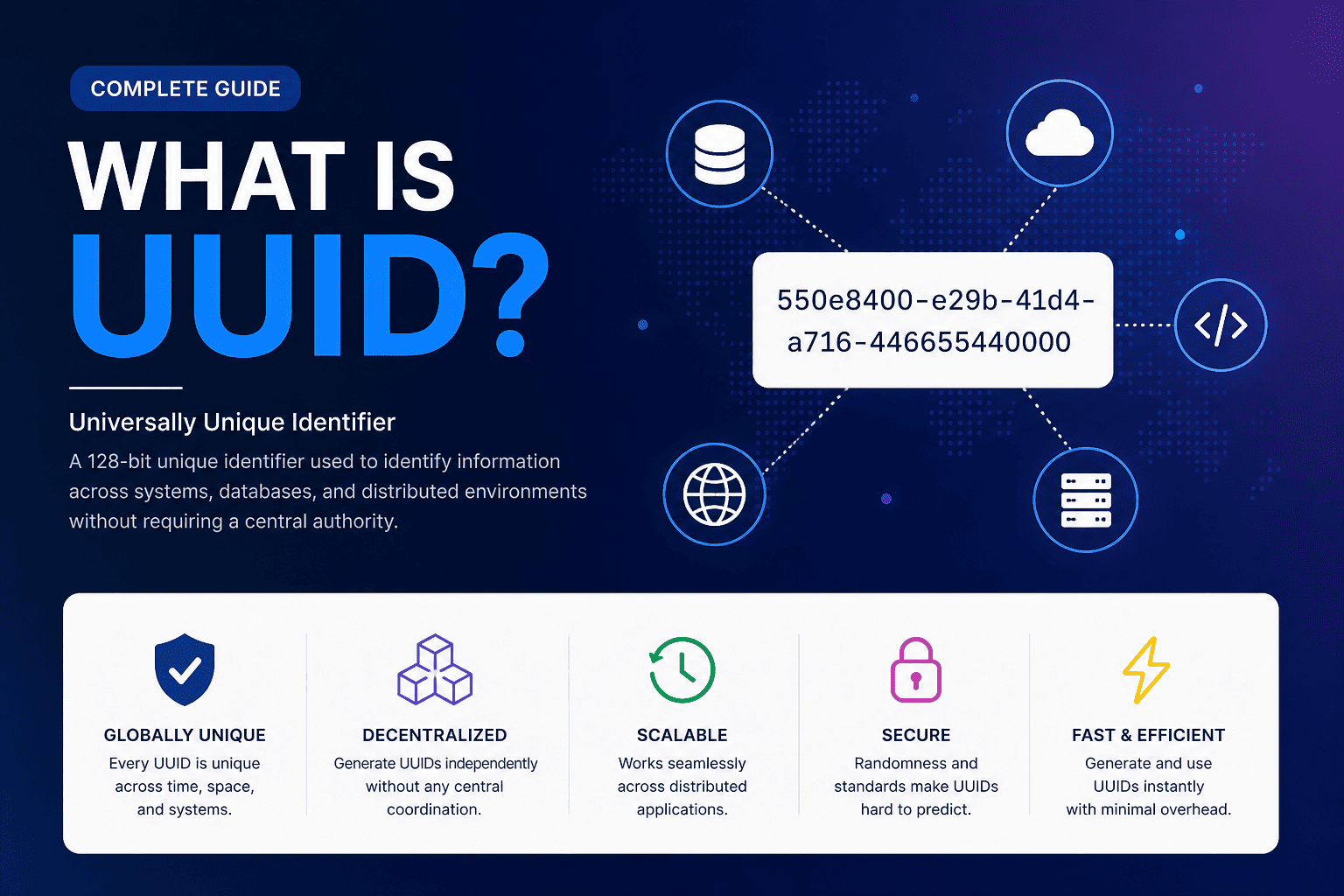
For application developers building authentication systems, consider using UUID v4 for session tokens and JWT for stateless authentication — both are covered by tools on this platform.
Privacy — Generated Passwords Never Leave Your Browser
Every password generated by this tool is created entirely within your browser using the Web Crypto API. No password, no configuration, and no usage data is ever transmitted to any server. The tool works fully offline — you can even save this page and use it without an internet connection.
This privacy-first approach is the same principle applied across all tools on this platform. For generating unique identifiers for your applications, explore our UUID Generator, ULID Generator, and NanoID Generator — all client-side, all zero server calls.