What is UUID? A Complete Beginner-Friendly Guide for 2026
Discover what UUID is, how it works, and why developers rely on it for database keys, API resources, and distributed systems. Complete guide with examples.
Ever wondered how Amazon keeps your shopping cart intact when you switch from desktop to mobile? Or how your database ensures every single record has a completely unique identifier without checking with a central server? The answer is UUID - Universally Unique Identifier.
If you're a developer, system architect, or working with databases and distributed systems, you need to understand UUIDs. This guide breaks down everything from basic concepts to practical implementation strategies.
In this guide, you'll learn:
What UUID is and why it matters for modern applications
How UUIDs differ from traditional sequential IDs
The different UUID versions (v1, v4, v5, v7) and when to use each
Real-world applications in e-commerce, APIs, and IoT
Practical code examples in Python, JavaScript, and Java
Common pitfalls to avoid when implementing UUIDs
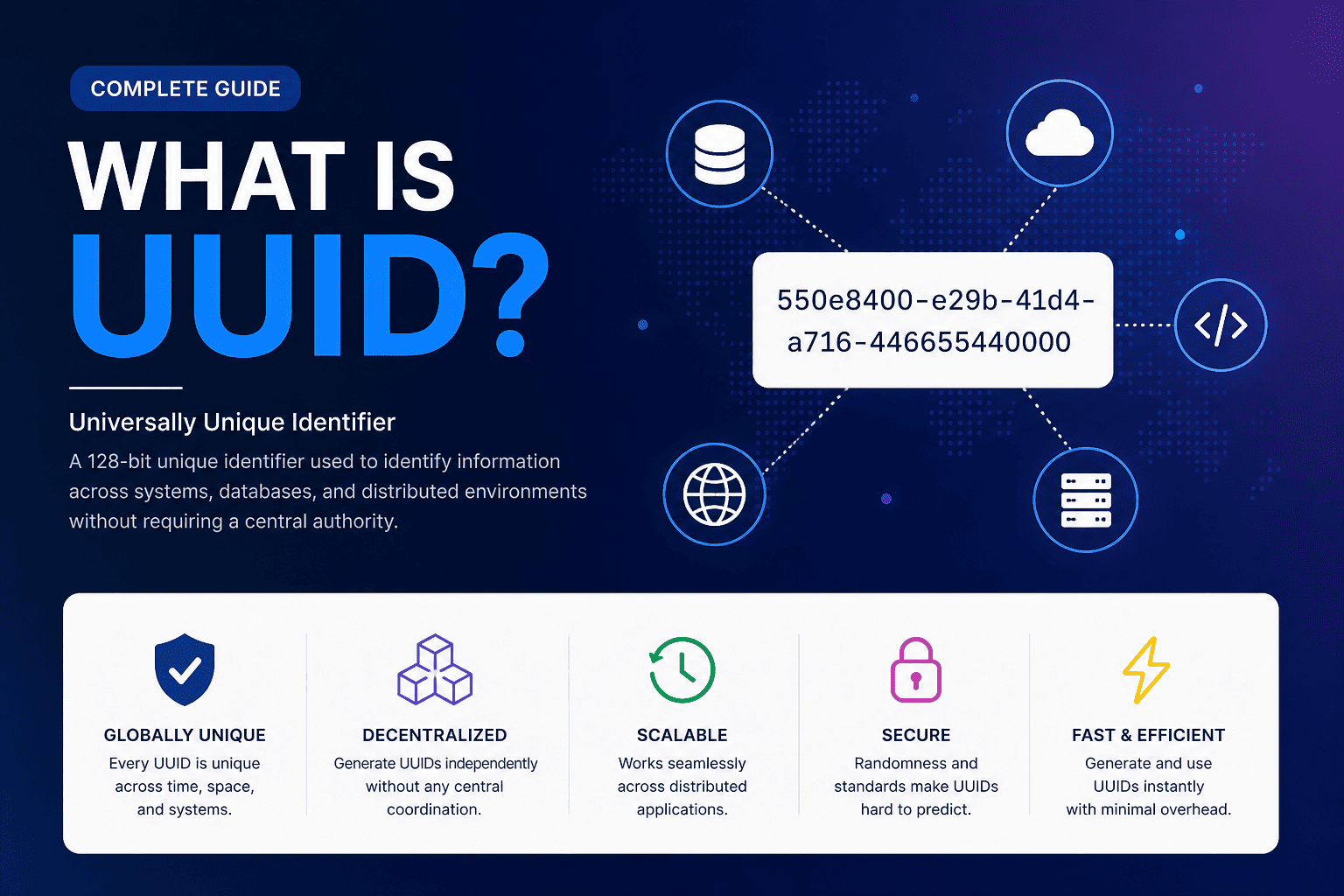
Understanding UUID: The Foundation
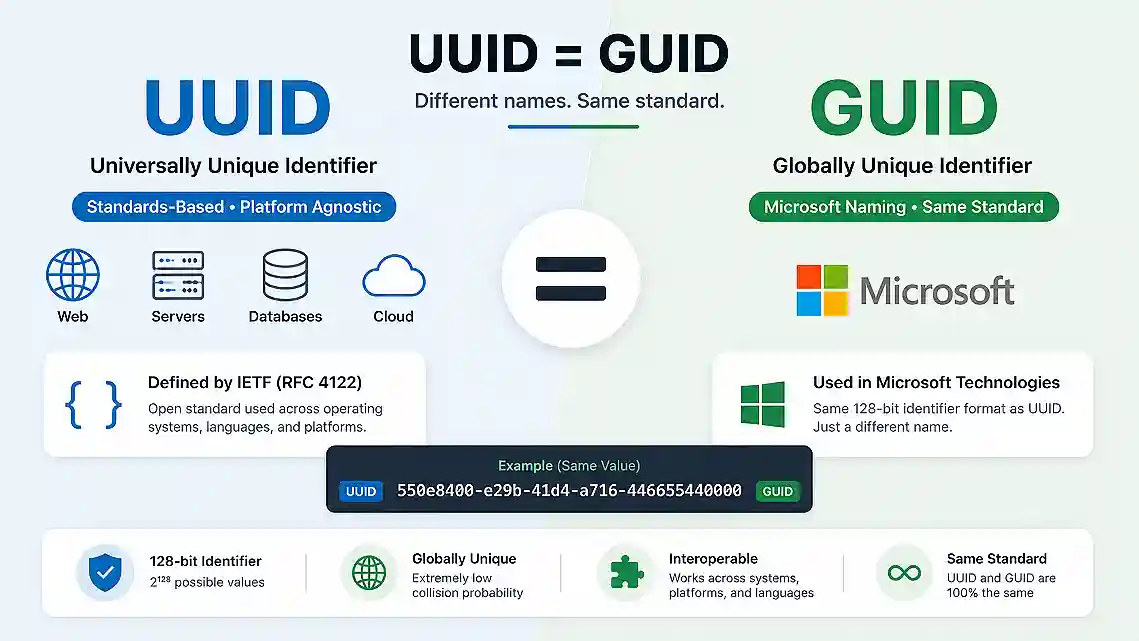
A Universally Unique Identifier (UUID) is a 128-bit number used to uniquely identify information in computer systems. Think of it as a digital fingerprint that's so unique you can generate billions of them across different systems without ever worrying about duplicates.
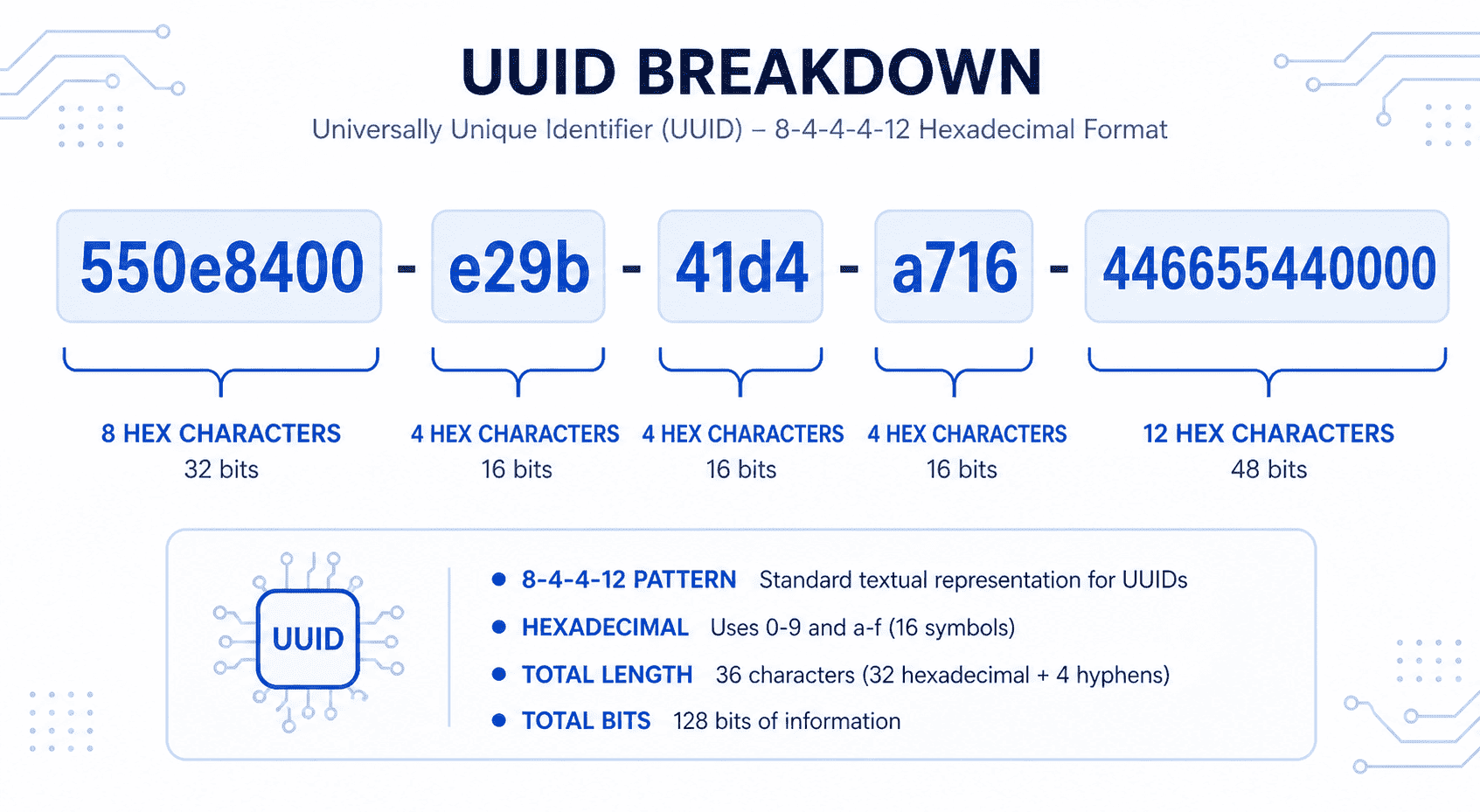
UUIDs follow a standardized format that looks like this:
This 36-character string consists of 32 hexadecimal digits (0-9 and A-F) separated by hyphens in a specific pattern: 8-4-4-4-12.
The Math Behind UUID Uniqueness
The brilliance of UUIDs lies in their scale. With 128 bits of data, there are 2^128 possible combinations - approximately 340 undecillion unique values (340 trillion trillion trillion). You could generate 1 billion UUIDs every second for 100 years and still have only a 50% chance of creating a single duplicate.
This near impossibility of collision makes UUIDs perfect for distributed systems where multiple servers need to generate unique identifiers simultaneously without coordination.
Why UUIDs Matter: Solving the ID Problem
Traditional identification systems rely on sequential numbering (1, 2, 3...) or centralized ID servers. These approaches create bottlenecks in distributed environments. UUIDs solve this by enabling decentralized ID generation.
Key Advantages of Using UUIDs
No Central Authority Required Computer systems generate UUIDs locally using very large random numbers. No coordination between different systems is needed, making UUIDs ideal for cloud-native applications and microservices architectures.
Globally Unique Across Systems UUIDs generated by independent parties can be merged into a single database without causing duplicate identifiers. This is invaluable when combining data from multiple sources or systems.
Enhanced Security and Privacy Unlike sequential IDs that expose information about your database size or record count, UUIDs are non-sequential and unpredictable, making them harder to guess or enumerate.
Perfect for Distributed Databases In distributed systems like CockroachDB or MongoDB, UUIDs allow each node to generate unique identifiers autonomously without waiting for a central server, eliminating performance bottlenecks.
The Different UUID Versions Explained
Not all UUIDs are created equal. There are eight officially recognized versions, each designed for specific use cases. Let's explore the most commonly used versions.
UUID Version 1 (v1): Time-Based Identifiers
Version 1 UUIDs combine three components:
A 60-bit timestamp (100-nanosecond intervals since October 15, 1582)
A 14-bit clock sequence
A 48-bit MAC address of the generating computer
Format Example:
Pros:
Naturally sortable by creation time
Guaranteed uniqueness per machine
Useful for time-ordered tracking
Cons:
Exposes your computer's MAC address (privacy risk)
Reveals precise creation timestamp
Can leak system information
When to Use: Version 1 is rarely recommended for modern applications due to privacy concerns. If you need time-ordered IDs, UUID v7 is the better choice.
UUID Version 4 (v4): Random Identifiers
UUID v4 is the most popular version, generating identifiers using cryptographically secure random numbers. Approximately 122 bits are random (6 bits are reserved for version and variant markers).
Format Example:
Pros:
Maximum privacy—no embedded system information
Simple implementation—just needs a random number generator
Widely supported across all programming languages
Unpredictable and secure
Cons:
Not sortable by creation time
Can cause database index fragmentation
No embedded metadata
When to Use: UUID v4 is the default choice for most applications. Use it for API keys, session tokens, user IDs, file identifiers, and any scenario requiring random, opaque identifiers.
UUID Version 5 (v5): Name-Based with SHA-1
Version 5 generates UUIDs deterministically by hashing a namespace UUID and a name string using the SHA-1 algorithm. The same input always produces the same UUID.
Code Example (Python):
Pros:
Deterministic - same input = same output
Useful for creating stable identifiers from existing data
No need to store mapping between names and UUIDs
Cons:
Not random - predictable from inputs
Uniqueness depends on input uniqueness
Not suitable for security-sensitive applications
When to Use: Use v5 when you need consistent UUIDs generated from existing data like email addresses, URLs, or usernames. Perfect for creating stable references without database lookups.
UUID Version 7 (v7): Modern Time-Ordered Identifiers
UUID v7 is the newest version, introduced in RFC 9562 (May 2024). It combines:
A 48-bit Unix timestamp in milliseconds
74 random bits
This design makes v7 UUIDs naturally sortable by creation time while avoiding the privacy issues of v1.
Pros:
Sortable by creation time for optimal database performance
No MAC address exposure
Excellent for B-tree indexes
Better database insert performance than v4
Cons:
Newer standard with limited library support
Reveals approximate creation time
When to Use: UUID v7 is highly recommended for new projects, especially for database primary keys, event streams, and any scenario where chronological ordering matters.
Real-World UUID Applications
UUIDs power countless digital experiences across industries:
1. E-commerce Shopping Carts
When you add items to your Amazon cart, a UUID tracks your specific cart session. This identifier ensures your cart persists across devices and browser sessions without requiring you to log in immediately.
2. Database Primary Keys
Distributed databases like CockroachDB and MongoDB use UUIDs as primary keys. This allows different database shards to insert records simultaneously without coordination, dramatically improving write performance.
Example (MySQL):
3. RESTful API Resource Identifiers
Modern APIs use UUIDs in resource URLs:
This approach provides security through obscurity - attackers can't enumerate resources by incrementing numbers.
4. Cloud File Storage
Services like AWS S3 and Google Cloud Storage use UUIDs to name uploaded files, preventing filename collisions even when millions of users upload files with identical names.
5. Session Management and Authentication Tokens
UUIDs create unpredictable session IDs that resist brute-force attacks. Their randomness makes them significantly more secure than sequential session identifiers.
6. IoT Device Identification
In large-scale IoT deployments, each sensor or device receives a UUID. This enables unique identification across billions of devices without centralized registration.
7. Blockchain and Distributed Ledgers
Blockchain systems use UUIDs for transaction IDs and block references, ensuring global uniqueness across the decentralized network.
Generating UUIDs: Practical Code Examples
Python Implementation
JavaScript Implementation
Java Implementation
UUID Decision Framework: Choosing the Right Version
Here's a practical decision tree for selecting the appropriate UUID version:
Ask yourself these questions:
Do you need sortable/chronological IDs?
YES → Use UUID v7 (modern) or v1 (legacy)
NO → Continue to question 2
Do you need the same UUID for the same input?
YES → Use UUID v5 (deterministic)
NO → Continue to question 3
Are you building database-heavy applications?
YES → Use UUID v7 (better performance)
NO → Use UUID v4 (default choice)
Quick Reference:
Default choice: UUID v4
Database primary keys: UUID v7
Deterministic IDs: UUID v5
Legacy systems: UUID v1 (avoid for new projects)
Common UUID Misconceptions and Pitfalls
Misconception 1: "UUIDs Are 100% Unique"
While collision probability is astronomically low, UUIDs aren't mathematically guaranteed unique. However, the chances are so infinitesimally small (approximately 1 in 5.3 × 10^36 for v4) that treating them as unique is practically safe.
Misconception 2: "All UUIDs Are Random"
Only UUID v4 uses purely random generation. Versions 1, 5, and 7 incorporate deterministic elements like timestamps or hashed names.
Misconception 3: "UUIDs Work as Security Tokens"
UUIDs are identifiers, not cryptographic secrets. Never use UUIDs as passwords, encryption keys, or in security-critical contexts where cryptographic properties are required.
Misconception 4: "Higher Versions Are Always Better"
Each UUID version serves different purposes. Version 7 isn't "better" than version 4—it's optimized for different use cases (database performance vs. maximum randomness).
When NOT to Use UUIDs
Despite their versatility, UUIDs aren't always the optimal choice:
User-Facing Identifiers UUIDs are not human-friendly. For order numbers, invoice references, or customer IDs that users will read and communicate, use shorter, readable formats like "ORD-2024-001234".
Strict Sequential Ordering Requirements If your application absolutely requires consecutive numbering with no gaps, traditional auto-increment integers are more appropriate.
Extreme Storage Optimization UUIDs consume 16 bytes (binary) or 36 characters (string). In systems with billions of records where every byte matters, this overhead could be significant.
Simple, Single-Server Applications For non-distributed applications running on a single database server, auto-increment IDs are simpler and offer better database performance without UUID's distributed benefits.
Database Performance Considerations
UUID v4 and Index Fragmentation
Random UUIDs (v4) can cause B-tree index fragmentation because new records aren't inserted at the end of the index. This leads to:
More page splits
Reduced cache efficiency
Slower write performance at scale
UUID v7 Performance Advantage
UUID v7 solves this problem by sorting chronologically. New records insert near the end of the index, maintaining sequential locality and dramatically improving database write performance.
Benchmark comparison (insertions per second):
Auto-increment INT: ~50,000/sec
UUID v4: ~15,000/sec (3.3x slower)
UUID v7: ~42,000/sec (only 1.2x slower)
Storage Optimization
Store UUIDs as binary(16) rather than char(36) to save 55% storage space:
The Future of UUIDs: RFC 9562 and Beyond
The UUID specification continues evolving. RFC 9562, published in May 2024, introduced three new versions:
UUID Version 6: Reordered version 1 for better database sorting UUID Version 7: Time-ordered with random data (recommended for new projects) UUID Version 8: Custom format for application-specific requirements
Industry adoption of UUID v7 is accelerating rapidly due to its excellent balance of uniqueness, sortability, and database performance.
Conclusion: Mastering UUIDs for Modern Development
UUIDs are fundamental infrastructure for modern software systems. They solve the critical challenge of generating unique identifiers without central coordination—making them indispensable for distributed systems, cloud applications, and microservices architectures.
Key Takeaways:
Start with UUID v4 for general-purpose unique identifiers
Use UUID v7 for database primary keys and time-ordered data
Choose UUID v5 when you need deterministic, reproducible IDs
Avoid UUID v1 in new projects due to privacy concerns
Store UUIDs as binary for optimal database performance
Never use UUIDs as cryptographic keys or passwords
Understanding when and how to use UUIDs empowers you to build scalable, distributed systems that can grow from thousands to billions of records without architectural changes.
Whether you're building e-commerce platforms, IoT networks, or enterprise SaaS applications, UUIDs provide the reliable, scalable identification infrastructure your systems need to thrive.
Ready to implement UUIDs in your next project? Start with UUID v4 for simplicity, then optimize with v7 when database performance becomes critical. The invisible infrastructure of unique identifiers will quietly power your application's growth for years to come.
Discussion
No comments yet
Be the first to share your thoughts.
Leave a Comment